Posted on March 10, 2022
Estimated reading time 4 minutes
A new standard of data security is set to revolutionise remote and hybrid working patterns. Identity management practices offer seamless workflows so employees can access the IT resources they need quickly without undermining security standards.
This article will discuss what Microsoft identity management is, what you’ll need to set it up, and how Azure identities support hybrid working demands. We’ll also consider how you can implement identity management in your organisation with best practices with help from a managed services partner. Read on to find out more.
What is Microsoft identity management?
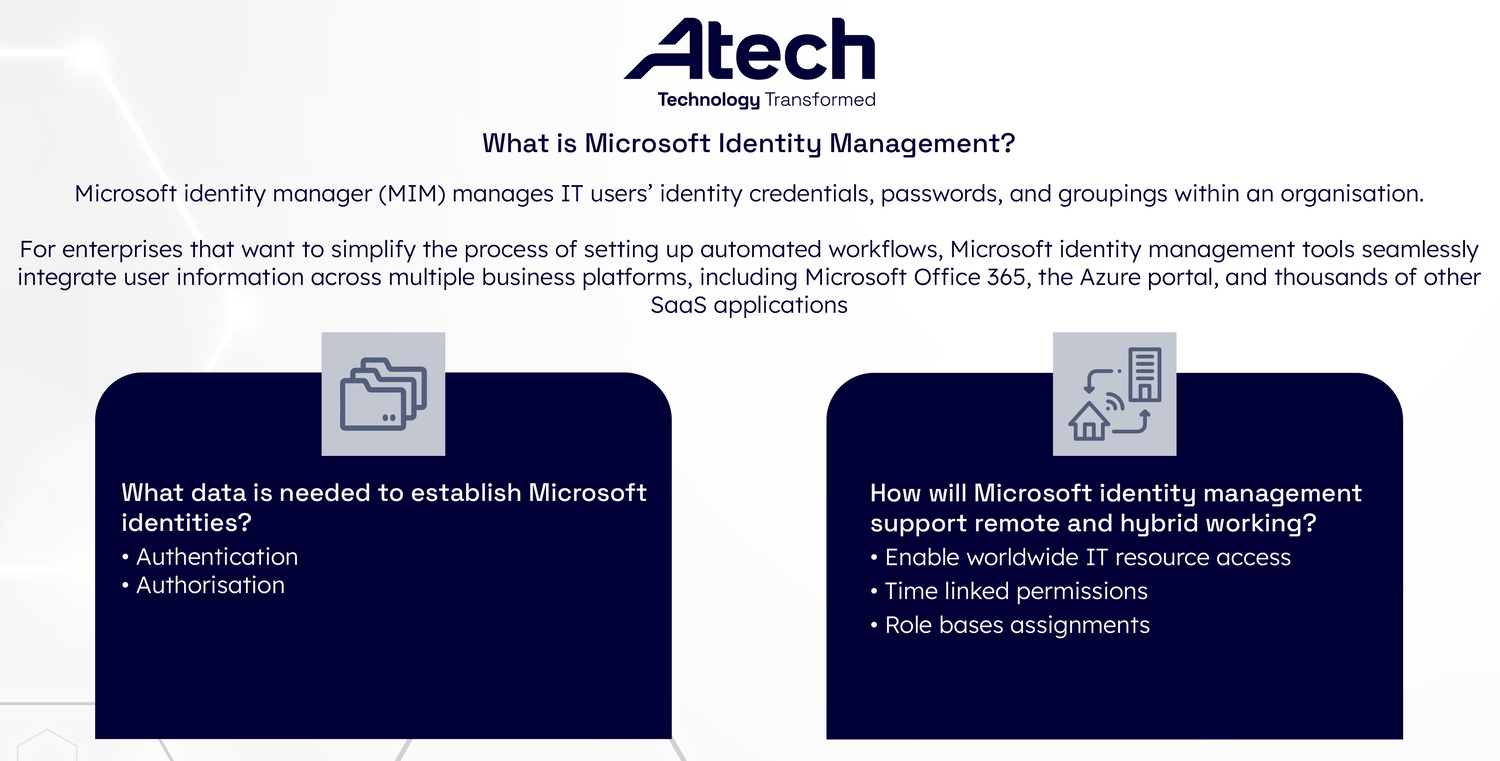
Microsoft identity manager (MIM) manages IT users’ identity credentials, passwords, and groupings within an organisation. It is an evolution of the Azure Active Directory (Azure AD) developer platform. Microsoft identity manager creates a dynamic process for ensuring timely and seamless user access to core IT tools without compromising security standards.
For enterprises that want to simplify the process of setting up automated workflows, Microsoft identity management tools seamlessly integrate user information across multiple business platforms, including Microsoft Office 365, the Azure portal, and thousands of other SaaS applications.
Microsoft Identity Manager can also oversee scenarios such as synchronising real-time data updates to directory information across all relevant systems. The software can also eliminate data entry processes and other user-management scripts an organisation might employ to transfer user information internally. Furthermore, organisations can use MIM to build customer-facing applications, allowing Microsoft and other social networking users to login in securely.
What sort of data do I need to establish Microsoft identities
Depending on your organisation’s needs, the data points required to establish identities in Microsoft ID management tools may vary.
Some of the core aspects that underpin identity management include:
Authentication
- What verification steps ahead of access permissions ( including multi-factor authentication and password policies) does your company need to protect information?
Authorisation
- What are the access requirements associated with each role within your organisation? For example, HR departments require access to sensitive employee information, whereas a sales team will need secure access to various financial details.
- Additionally, organisations need to consider their permission to read, write, and share relevant data across multiple departments.
Based on the above-listed attributes, organisations can categorise users into two main groups, those who need to maintain a cloud-only identity and those who require a hybrid identity model within Microsoft identity manager.
Cloud-only user IDs can be created within the Azure AD tenant of your Microsoft 365 subscription. The key advantage of Azure managed identity protocols is that no extra server or directory tools are required to log user information. You do not need to authenticate users on an on-site Active Directory Domain Service (AD DS).
Alternatively, hybrid identity models work well for companies with existing AD DS services or those who use an alternative ID provider. Under the hybrid management model, the Azure AD tenant automatically sends authorisation data to your ID provider, allowing users to access on-premises IT tools and cloud-based resources under one login.
How will Microsoft identity management support remote and hybrid working?
Identity-enabled cloud security supports many remote working demands.
For example, firms enabling worldwide access to IT resources can set up smart travel policies that attract and retain the best talent. Expanding a company’s potential to hire abroad with the right access tools can also help businesses speed up production cycles and effectively set up business operations that can run 24 hours a day.
Also, time-linked permissions accommodate employees with flexible schedules (building a positive workplace culture, as employees adjust their working hours to maintain a healthy work/life balance).
Moreover, role-based assignments simplify the onboarding process. Businesses can streamline training processes and build employee motivation by providing instant access to just the tools and permissions a new employee needs. New starters using MIM support will see all of their software tools ‘just work’ in the background without users having to log ID credentials across multiple sites repeatedly.
What are some of the best practices around identity management?

To maintain sound identity management processes within an organisation, senior leaders must ensure that they are keeping up with identity management best practices. These include:
Regular permission audits
Time-limited access to IT resources:
- Matching access needs to operational hours
- New user permissions are provided only for as long as necessary
Automated security protocols (e.g., blacklisted IP addresses, password resets)
Outsourced cloud management support:
- Access to specialist security skills at affordable rates for medium and small organisations
- Dedicated technical support and tailored services
How can senior stakeholders communicate the importance of identity management to employees best?
To help employees grasp the relevance of identity-management protocols, it may be helpful to draw parallels between enterprise identity management and personal security practices used in other aspects of their online lives. Employees come into contact with identity verification protocols daily on social media platforms, email accounts, and personal devices. Microsoft and Azure identity management work in the same way, the process is streamlined to one authorization process rather than several.
Senior business leaders should emphasise the message that identity management practices enable seamless workflows for employees. Furthermore, identity management methods provide senior leaders with traceability over company data. If things go wrong, it’s easy to identify and address the issues.
Get started with Microsoft identity management
Move past the traditional perimeter-based security model and equip your workplace with the new standard of data security: identity management.
By adopting a cloud-first approach, you can help you simplify your IT management needs and empower your employees to work flexibly, all while ensuring your files and software are secure from breaches.
Microsoft identity management tools offer intelligent ways to maintain just-in-time access to your IT resources — whether it’s syncing access permissions with your operational hours or onboarding new hires from across the globe.
Transform your business with identity management best practices, access expert support from a managed services partner, and maintain a highly optimised cloud-enabled business.
Access tailored Azure managed identity support with Atech
Atech is a leading UK Azure cloud services provider and a multi-Gold Microsoft partner.
With over 10,000 servers migrated or refactored in Azure, we help our clients transform their cloud infrastructure to maintain a secure and agile technology ecosystem.
We deliver a unified SecOps strategy using Azure Sentinel and Azure Defender to create a seamless Zero Trust network across your organisation. You can access tailored Azure identity management support and secure your data with Microsoft best practices by working with us.
Get in touch to learn the next steps in addressing risks and opportunities in your cloud infrastructure and discover new ways to streamline your business today.